
10 years ago this week I published this blog post while @cptjesus.bsky.social, @harmj0y.bsky.social and I were working on what eventually became BloodHound: wald0.com?p=14

10 years ago this week I published this blog post while @cptjesus.bsky.social, @harmj0y.bsky.social and I were working on what eventually became BloodHound: wald0.com?p=14
Next week I'll be speaking at WWHF Mile High in Denver about Abusing Backup Operators with @trustedsec.com's Titanis.
web.cvent.com/event/1dbf78...

SCCM attack paths are messy until you can see them. 👀
ConfigManBearPig from Chris Thompson extends BloodHound with SCCM nodes + edges using OpenGraph, plus queries to surface hierarchy takeovers and escalation paths.
Check it out: ghst.ly/45FCP5G

Note: Work related
I do Active Directory stuff for a living. Security research to be more specific. One of my favorite niche AD topics is AdminSDHolder. It's even my vanity domain.
I wrote a 159 pg book about AdminSDHolder. I'm kinda proud of it.
specterops.io/resources/ad...

See your network shares the way attackers do. 👀
Meet ShareHound, an OpenGraph collector for BloodHound CE & Enterprise that reveals share-level attack paths at scale.
@podalirius.bsky.social unpacks all the details in our latest blog post. ghst.ly/4ogiBqt
Incredible to see @hdm.io using BloodHound to build the new runZeroHound, connecting asset inventory data from
@runzero.com with attack path visualization.
Love seeing the community take BloodHound in new directions!

Credential Guard was supposed to end credential dumping. It didn't.
Valdemar Carøe just dropped a new blog post detailing techniques for extracting credentials on fully patched Windows 11 & Server 2025 with modern protections enabled.
Read for more: ghst.ly/4qtl2rm

Introducing PingOneHound! This OpenGraph extension for BloodHound can help you identify, analyze, execute, and remediate attack paths in PingOne organizations. Read the introductory blog post here: specterops.io/blog/2025/10...

@reconmtl.bsky.social has uploaded the majority of the 2025 talks, including my talk on LSA. You can check it out at the below link if you'd like.
Thank you again to the organizers and everyone else who helps put on the conference. I look forward to coming back!
youtu.be/G2CfMWXLU1U?...
Check out my new blog diving deeper into BroCI.
I'd also love to add calls to native Win32 APIs to this graph, the on-disk binaries themselves and the permissions against them, COM object instantiation/calling, etc.
At that point I see this graph being capable of assisting with the discovery of currently unknown "lolbin" primitives.
This obviously does not guarantee that a function called from one of these binaries will land at a function in kernel32.dll. I'd love to map cross-binary function call graphs. Not sure whether there is an easy solution to that.

A little OpenGraph POC for mapping PE header imports of all .dll and .exe files in a fresh Windows install. These are all the binaries that have some kind of import chain leading to kernel32.dll
This is the kind of research that should invite serious conversation about the trustworthiness of cloud authentication services.
It won't. But it should.
I've been researching the Microsoft cloud for almost 7 years now. A few months ago that research resulted in the most impactful vulnerability I will probably ever find: a token validation flaw allowing me to get Global Admin in any Entra ID tenant. Blog: dirkjanm.io/obtaining-gl...

Adalanche searches works way better now - it uses BFS rather than DFS which gave unnecessary long paths at times. This is available in the latest commit on GitHub.
There might be bugs with the new search - let me know if you see any strangeness. Happy hunting :-)

We've got a fresh #BloodHoundBasics post from @jonas-bk.bsky.social!
Ever wondered about those obscure AD special identity groups that quietly grant permissions to every principal in your environment?
With BloodHound, you can uncover compromising permissions tied to these groups.
🧵: 1/2

BloodHound isn't just for Active Directory anymore. 🤯
@sadprocessor.bsky.social dives into the BloodHound OpenGraph functionality & demonstrates the new PowerShell cmdlets added to the BloodHound Operator module to work with the OpenGraph feature. ghst.ly/4peTTrB

From November 2016:
This is how I used to design BloodHound's entity panels. Just a text editor to list out what I as a red-teamer wanted to see, with the corresponding (then new) cypher queries listed as well.
Simple, VERY low-fidelity mockup, but really helped during the design phase.

🚨 New #BloodHound shirt alert 🚨
✅ - Unisex adult/child and ladies sizes available
✅ - Cool design :)
✅ - ALL profits go to charity
This time we are supporting Hope for HIE, which supports families suffering the effects of hypoxic ischemic encephalopathy
Get your shirt here: ghst.ly/bh8-tshirt
Such a fantastic find and the ideal outcome. Amazing work, Katie.
Check out my new blog on nested app authentication.
Gonna tell my kids this is the eras tour
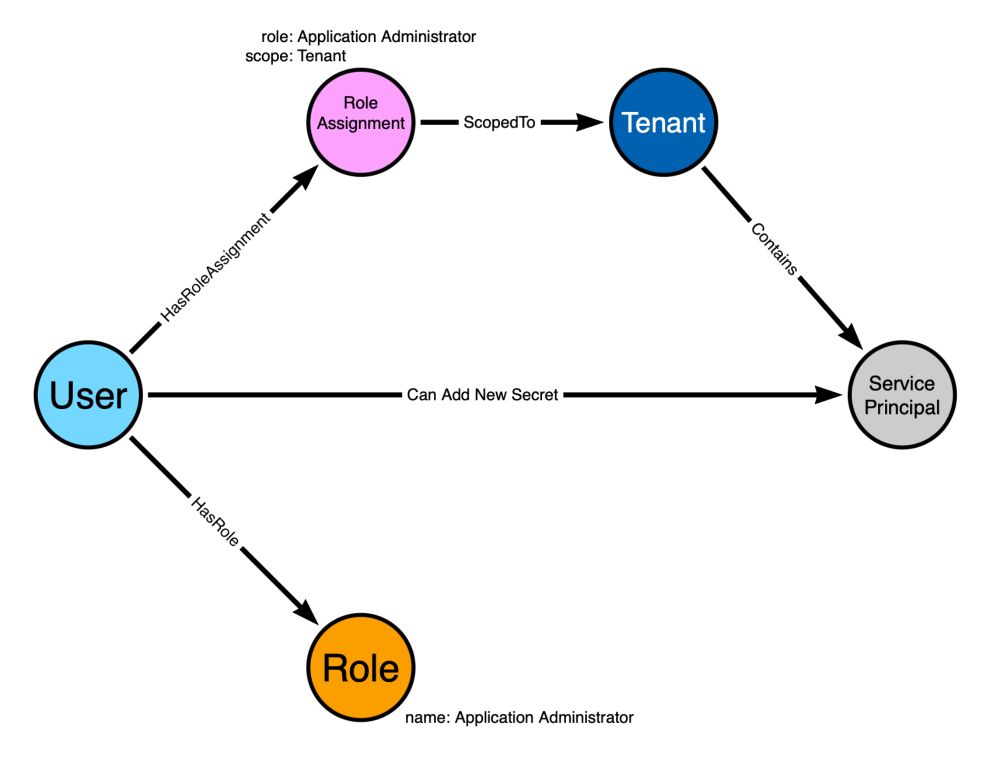
In this blog post I explain the fundamental building blocks, vocabulary, and principles of attack graph design for BloodHound: specterops.io/blog/2025/08...
Drive safe
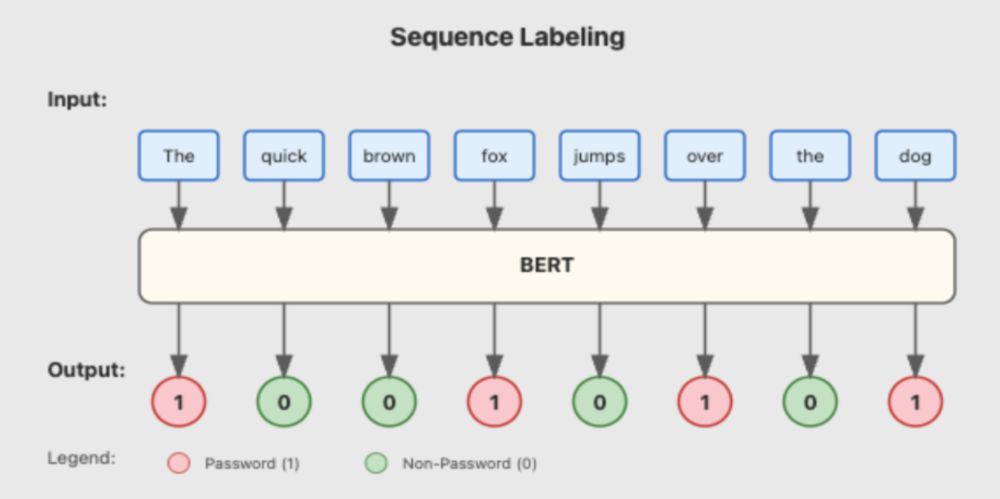
Red teamers know the drill: endless file churning, hunting for passwords & tokens. 🔍
Meet DeepPass2, our new secret scanning tool that goes beyond structured tokens to catch those tricky free-form passwords too. Read Neeraj Gupta's blog post for more. ghst.ly/40HLNNA

Entra Connect sync accounts can be exploited to hijack device userCertificate properties, enabling device impersonation and conditional access bypass.
@hotnops.bsky.social explores cross-domain compromise tradecraft within the same tenant.
Read more: ghst.ly/3ISMGN9
@egyp7.bsky.social Hey dude ✌️
BloodHound v8.0 is here! 🎉
This update introduces BloodHound OpenGraph, revolutionizing Identity Attack Path Management by exposing attack paths throughout your entire tech stack, not just AD/Entra ID.
Read more from Justin Kohler: ghst.ly/bloodhoundv8
🧵: 1/7
Great minds