I'm looking for someone who has received one of the ominous unsolicited Instagram password reset e-mails around December 30, last year. I'd like to cross-check their Instagram data with the recent "leak". Appreciate a boost!
13.01.2026 12:40
👍 3
🔁 4
💬 0
📌 0

A recent leak of the BreachForums user table gave interesting insights into the most popular e-mail providers for Breached.
By far the most accounts are on Googlemail (n=240736), followed by Proton (n=43319). 9th most popular is DNMX (n=2077), followed by the long tail (n=12418).
12.01.2026 09:33
👍 0
🔁 0
💬 0
📌 0

Sorry, this could not wait until next #diday - I just deactivated my X account. The recent shitshow around Grok creating deepfake thirst traps is just too appalling.
Here's hoping that Bluesky won't suffer the same fate of enshittification.
09.01.2026 09:44
👍 3
🔁 0
💬 0
📌 0

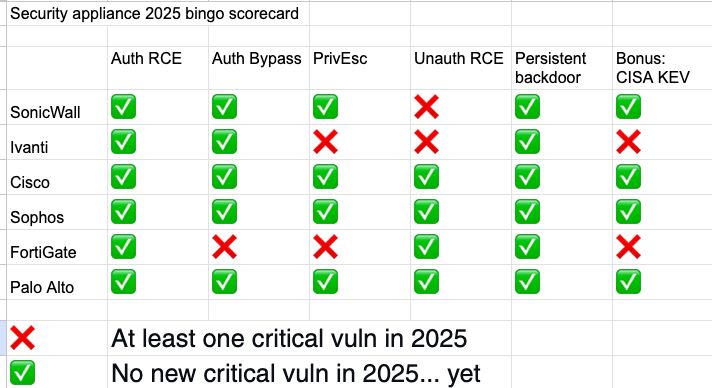
Nominees for the insecurity appliance bingo 2026
Let's try and crowdsource this. A couple candidates are a given:
- Fortinet, the 2025 winner
- Ivanti, the runner-up
One comment for each vendor who you'd like to include, and I'll try to count each "like" for that comment as one vote for the vendor.
07.01.2026 15:14
👍 1
🔁 0
💬 0
📌 0
Just out of curiosity - the speaker's russian sounds very indistinct, almost slurred, to me. Is this normal colloquial Russian or does he have some kind of accent? Or is he just mumbling a little?
21.11.2025 08:22
👍 3
🔁 0
💬 0
📌 0

BINGO TIME! With CVE-2025-58034, Fortinet secures the crown in my Insecurity Appliance Bingo. This is technically a "high" severity vuln, but since it's being actively exploited and has landed a spot on CISA KEV, I'm admitting it.
cku.gt/appbingo25
21.11.2025 06:53
👍 4
🔁 0
💬 0
📌 0
👋
18.11.2025 15:17
👍 1
🔁 0
💬 0
📌 0
The "ls -laR" of the Red Hat data breach by Scattered Lapsus$ Hunters -- err Crimson Collective -- is, put into a text file, 2 GB. That's a heck of a breach.
% wc -l REDHAT_GIT_LS.txt
37665671 REDHAT_GIT_LS.txt
06.10.2025 13:54
👍 0
🔁 0
💬 0
📌 0
No need to blur the IDs, they are just transaction IDs. I neber publish images with valid PII.
Valve stated that they aren‘t traceable to Steam user accounts - the only traceable info is phone numbers.
15.05.2025 11:00
👍 2
🔁 0
💬 1
📌 0
Selbst Netscape Communicator war schon ein CPU hog, IIRC…
17.04.2025 12:25
👍 0
🔁 0
💬 0
📌 0
Kategorie „Artikel, deren Titel sich seit 1996 nicht geändert hat“. 😅
17.04.2025 08:35
👍 1
🔁 0
💬 1
📌 0

After the impending CVE blackout: EU vulnerability database goes live
European cybersecurity authority ENISA, its US-counterpart CISA and others are positioning themselves to maintain continuity.
OK, interesting day so far. A lot of different ideas, initiatives and possible solutions to the MITRE CVE blackout are being floated and I kind of lost track. So I wrote it down here: heise.de/-10354564
Time will tell what happens, and I'll update the article as soon as official info is out.
16.04.2025 15:12
👍 1
🔁 1
💬 0
📌 0

Nach drohendem CVE-Aus: Schwachstellendatenbank der EU geht an den Start
Neben der EU-Cybersicherheitsbehörde ENISA positionieren sich unter anderem eine CVE-Stiftung und die US-Behörde CISA, um die Kontinuität zu wahren.
Interessanter Tag mit vielen Ideen und neuen Konzepten (und sogar einer neuen Schwachstellendatenbank) zu CVE/MITRE. Ich habe das Ganze mal mit dem Stand von ca. 16h aufgeschrieben:
heise.de/-10354324
Wenn sich was tut, versuche ich noch zu updaten.
16.04.2025 15:11
👍 1
🔁 0
💬 0
📌 0

I have upgraded the Insecurity Appliance Bingo to reflect the recent FortiNet advisory about a persistent backdoor. I also decided to include the Palo Alto Auth bypass CVE-2025-0108 in the bingo although it's not a "critical" (but barely). It is being actively exploited.
cku.gt/appbingo25
15.04.2025 12:24
👍 3
🔁 1
💬 0
📌 0

Le Pen: Berufungsgericht will 2026 über Unwählbarkeit entscheiden
Kann Rechtspopulistin Marine Le Pen doch noch bei den französischen Präsidentschaftswahlen 2027 antreten? Nach dem umstrittenen Kandidaturverbot kündigt das zuständige Gericht ein zügiges Berufungsver...
Hallo @spiegel.de, es ist übrigens auch false Balancing, alles, wogegen rechte Spinner schimpfen, als "umstritten" zu framen. Le Pen wurde nach geltendem Recht verurteilt, nur weil in Faschisten-Kneipen dagegen gewettert wird, steht dieses Urteil nicht in Zweifel.
www.spiegel.de/ausland/le-p...
01.04.2025 19:15
👍 1540
🔁 331
💬 31
📌 6
The customer list is almost certainly comprised of domain parts of e-mail addresses. There are domains like "fakeemail123.com" in there, most freemail providers and also fbi[.]gov - it's unscrubbed stuff with lots of fake info (for free Oracle Classic Cloud test accounts, I guess).
02.04.2025 09:27
👍 2
🔁 0
💬 0
📌 0
Das Testmuster liegt noch vor mir auf dem Tisch, ganz überzeugt war ich allerdings nicht. Mein guter alter Flipper ist mir dann doch näher. Habt Ihr interessante Spielereien mit dem T-Embed CC1101 (und Bruce/Capibara) auf Lager?
02.04.2025 09:22
👍 0
🔁 0
💬 0
📌 0

At long last (two weeks without a critical vuln!), there's a new insecurity appliance entry. And it's... *drumroll* Ivanti again! With an almost classic Auth RCE due to a stack-based buffer overflow (CVE-2024-22467), they are creeping into Bingo territory. Only two more cells to go!
12.02.2025 08:24
👍 2
🔁 0
💬 0
📌 0

Palo-Alto: Sicherheitslücken in Firmware und Bootloadern von Firewalls
Die Firmware und Bootloader von einigen Palo-Alto-Firewalls weisen Sicherheitslecks auf, die Angreifern das Einnisten nach Angriffen ermöglichen.
heise.de/-10257031 Firmware- und Bootloader-Bugs. Aber alle nicht "kritisch", daher füge ich sie erst einmal nicht ins Bingo-Sheet ein. Wenn jetzt natürlich jemand diese Bugs mit einem anderen verketten und eine Exploitchain mit persistenter Backdoor bauen würde...
27.01.2025 08:47
👍 0
🔁 0
💬 0
📌 0
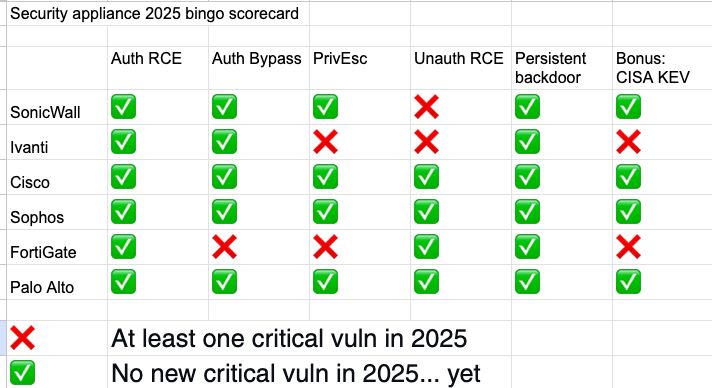
We have a new entry in the #2025securitybingo - SonicWall has an interesting RCE opportunity in their SMA1000 series. 9.8/10, that merits inclusion on my bingo card.
Three vendors down, three to go. We're halfway there!
23.01.2025 15:22
👍 2
🔁 0
💬 0
📌 0
Da Christian Anfall bei soviel Namensähnlichkeit!
17.01.2025 08:43
👍 4
🔁 0
💬 0
📌 0

A Series Of Unfortinet Events:
There's a bunch of new CVEs, at least one of them critical. There's an attack campaign against unsecured web UIs. Aaaand there's a leak of fifteen thousand config files plus VPN passwords. I took a closer look here: www.heise.de/en/news/Unkn...
15.01.2025 18:29
👍 1
🔁 0
💬 1
📌 0

Latest version of the 2025 (in)security appliance bingo adds CVE-2024-55591 / FG-IR-24-535 to the list. Thanks to watchTowr for reporting it, and thanks to various Fediverse users for alerting me to it. cku.gt/appbingo25
FortiNet admins: Go and patch your stuff. This is being exploited ITW.
15.01.2025 07:54
👍 0
🔁 0
💬 0
📌 1
makeagif.com/i/PBcpvS
13.01.2025 08:22
👍 0
🔁 0
💬 0
📌 0
So in etwa beginnt das „Erwachen“ in Shadowrun IIRC: Vulkanausbrüche in der Eifel. Next up: Ein Drache. Nicht, dass es mich noch besonders wundern würde…
11.01.2025 10:38
👍 2
🔁 0
💬 1
📌 0
This sounds like they are taking the phrase "dead letter box" a little too literally.
10.01.2025 08:41
👍 7
🔁 0
💬 0
📌 0

Does a new phishing scam allow PayPal accounts to be taken over?
In a blog article, a victim describes the criminals' approach. It cannot be traced, but Paypal may have already reacted.
I have seen numerous news items about the purported "new PayPal account takeover attack".
To any of the people who wrote said items: Have you tried the attack vector?
I have, and I cannot reproduce the attack. There are various screen shots here: heise.de/-10234666
Is this a hoax? Fixed?
10.01.2025 08:40
👍 2
🔁 0
💬 0
📌 0

Last bingo post for today, I promise.
I fleshed this out a little more. You can find the (In)Security Appliance Bingo 2025 in proper, two-dimensional form here:
cku.gt/appbingo25
Suggestions and submissions very welcome.
09.01.2025 14:30
👍 1
🔁 0
💬 0
📌 0
(In)Security appliance critical vuln list, 2025 edition, first issue, v3:
✅ SonicWall
❌ Ivanti
✅ Cisco
✅ Sophos
✅ FortiGate
✅ Palo Alto
(X means pwned, check mark means "not pwned yet".)
Only new vulns, only critical vulns. Vendor CVSS score counts unless it's clearly wrong.
09.01.2025 13:42
👍 0
🔁 0
💬 1
📌 0
(In)Security appliance critical vuln list, 2025 edition, first issue, v2:
❌ SonicWall
❌ Ivanti
✅ Cisco
✅ Sophos
✅ FortiGate
✅ Palo Alto
(X means pwned, check mark means "not pwned yet".)
Only new vulns, only critical vulns. Vendor CVSS score counts unless it's clearly wrong.
09.01.2025 13:35
👍 1
🔁 0
💬 0
📌 0