
Efabless is shut until further notice! Read this post to find out how past, current and future shuttles will be affected.
www.linkedin.com/posts/tinyta...

Efabless is shut until further notice! Read this post to find out how past, current and future shuttles will be affected.
www.linkedin.com/posts/tinyta...

Glad to see we’re able to reach a larger audience! The Chinese version of our book is doing well. @oflynn.com /ht Haisu Lee (our translator)
Great presentation, glitching the RPi 2350 on an unprotected path (USB VDD, they glitch protect others) to disturb reading critical OTP permission bits to mistakenly enable unsecured RISC-V cores to mess with TrustZone secured ARM cores without any limitations.
streaming.media.ccc.de/38c3/relive/...
events.ccc.de/congress/202...
You can bypass security on the RP2350 by glitching the OTP power supply (which does not have a glitch detector on it). This causes OTP to supply "guard data" instead of real data, and interpreting the guard data happens to enable RISC-V mode, which can do anything.
Yet another DMA form factor… Proper use of the IOMMU remains the primary mitigation.
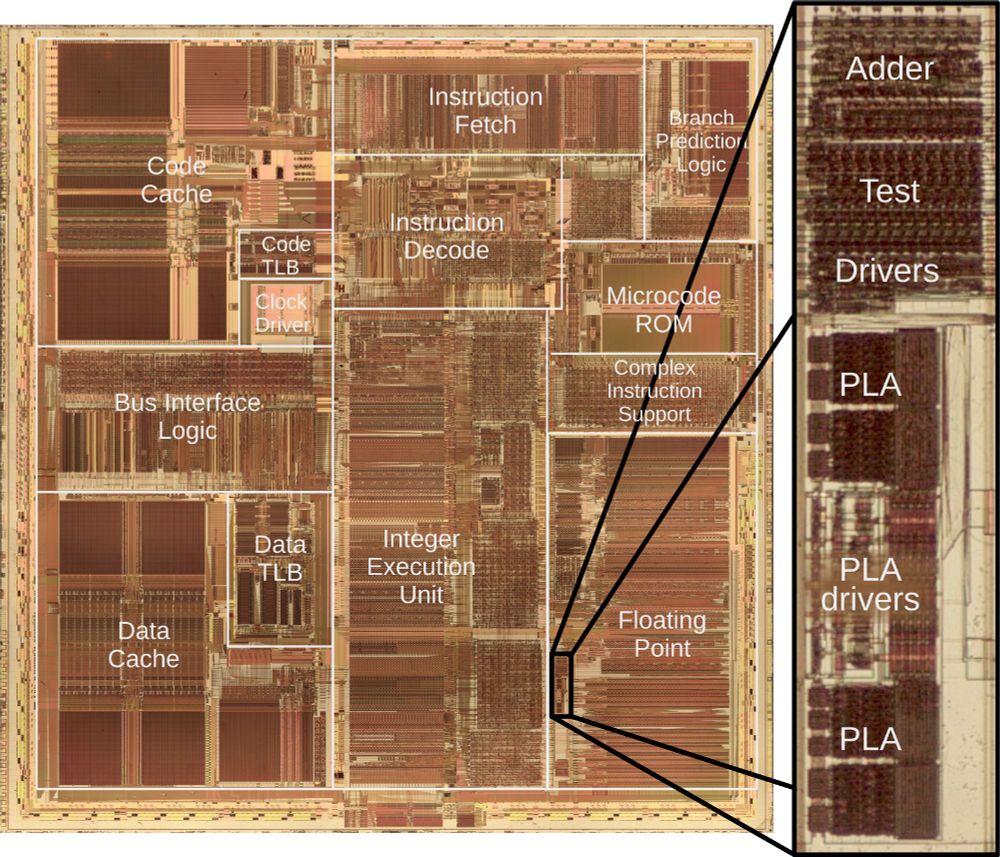
A die photo of the Pentium processor with the main functional blocks labeled including the caches, instruction fetch and decode, integer execution, and floating point. The image consists of complex patterns of rectangular regions in reddish and brownish colors. The image zooms in on a small part of the floating point unit giving a detail of an adder and PLA circuit.
Intel launched the Pentium processor in 1993. Unfortunately, dividing sometimes gave a slightly wrong answer, the famous FDIV bug. Replacing the faulty chips cost Intel $475 million. I reverse-engineered the circuitry and can explain the bug. 1/9