Why do you think they all wear masks?
Why do you think they all wear masks?

New from 404 Media: ICE is using a new facial recognition app to identify people, leaked emails show. Point camera at person, reveal their identity. It uses the CBP system that records peoples' faces as they enter or exit the U.S. Now, turned inwards to be used by ICE www.404media.co/ice-is-using...

Full guide covers OpSec, burner phones, data protection, secure communications, and handling law enforcement interactions.
Read: www.privacyguides.org/articles/202...
Key takeaways: Use strong passphrases to unlock phone, minimize stored data, prefer Signal for messaging, know your legal rights, and consider leaving your main phone at home entirely. #LA #Protests #ICE #DigitalRights #ProtestSafety #OpSec #PrivacyMatters
With recent protests and the documented surveillance conducted by law enforcement with aerial drones, protecting your digital privacy has never been more critical. Your smartphone can be both a powerful tool for coordination and documentation, and a significant security risk if not secured. 🧵👇

New from 404 Media: here's our report on the aircraft circling above the LA protests. Local, state, DHS, military all flew. Left: aircraft from air base. Right: a distinctive high altitude/hexagonal flight pattern, looks like a Predator drone (it flew to border after) www.404media.co/dhs-black-ha...

A picture worth 0x3E8 words at Bsides Seattle. @00wham.bsky.social
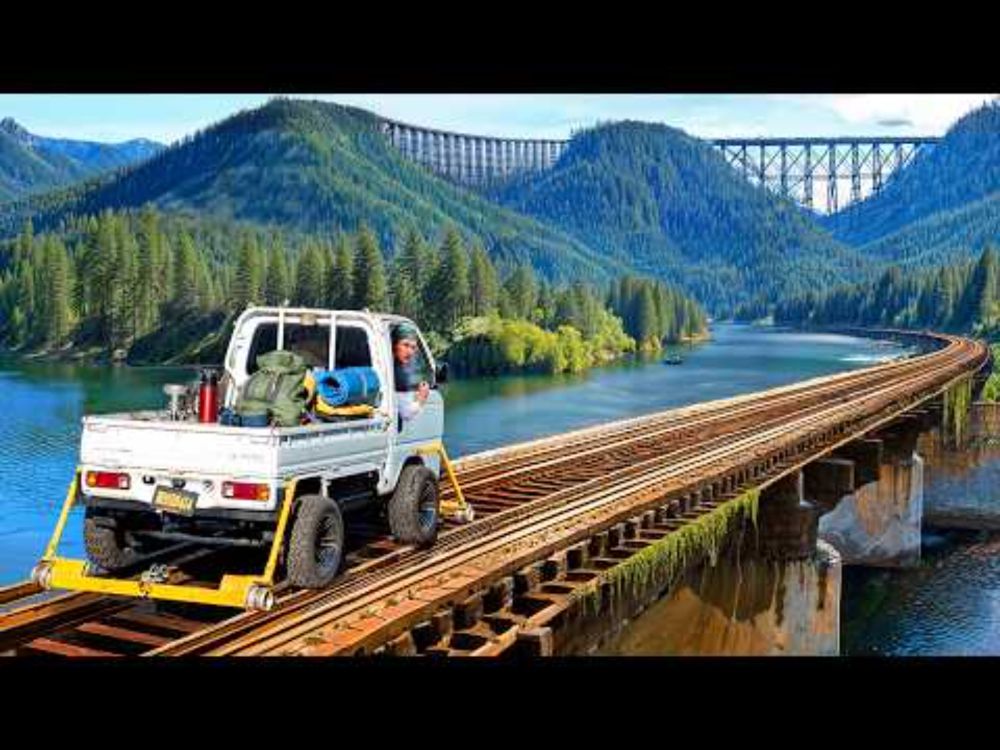
Here's part one of his 3-part series. The series is great, but overall PrestonGoes is one of the best YouTube channels I've found. He's an incredibly genuine and positive guy and his videos are fun to watch.
youtu.be/FgOJwFLF26k?...
@abyssdomainexpert.bsky.social Absolutely loved your talk at HC Seattle last year. When I heard the @jackrhysider.bsky.social episode, I had to do some digging to see if it was the same person or someone else with an identical story lol. Glad to find you on here.

Thank you Jack Rhysider and @DarknetDiaries for letting me tell the Bike Index story darknetdiaries.com/episode/153/
Well that was incredibly creepy lol. Nice work!
Ok, this is brilliant. @sirocyl.bsky.social set up a DTMF bomb on their voicemail message to spam DTMF tones to spammers and jam up their PBX systems. They accidently broke Ikea.
cohost.org/sirocyl/post...
“if you don’t have a family then make one” okay fine im making an ai family for the holidays
No I haven't had to log in since creating my account 🤷♂️
@fixit42.bsky.social Heya FixIt! 💜
the friends of cabal starter pack!
go.bsky.app/JAR9jhy
No, not personally. This was one of the challenges on OWASP's WebGoat, and I figured I'd make a post about it.
@owasp.org too
@johnhammond.bsky.social should definitely be on this list. He puts out great content.

Shout out to @owasp.org and github.com/WebGoat/WebG... for putting together this great example!
Tips to stay safe from cookie hijacking:
✅ Websites: Use random, encrypted session cookies over HTTPS.
✅ Users: Log out after use, enable MFA, and avoid untrusted networks. Protect your cookies and keep hackers out! 🔐

We intercept the login request as Admin, swap in the cookie we created for Tom, and boom — we're logged in as him! 🕵️ This is cookie hijacking in action. Weak session cookies can expose accounts. Secure cookies save lives! 🛡️


The decoded cookies reveal plain text:
Webgoat: nzozZtxkdKtaogbew
Admin: nzozZtxkdKnimda
Reversing these strings, we see the username is reversed at the end.
To impersonate Tom, we reverse “Tom,” encode it in hex, then Base64. Crafting Tom’s session cookie lets us hijack his account! 😱

Authentication cookies like spoof_auth are often Base64 encoded. If predictable, they can be exploited! Logging in with credentials we know of such as Webgoat and Admin, we find:
Webgoat: NmU3YTZm...
Admin: NmU3YTZm...
Decoded, these cookies reveal hex patterns. Time to exploit them! 🔓
What is cookie hijacking? 🍪🔒
Authentication cookies keep you logged in, but if they're predictable, hackers can use them to impersonate you. Let’s explore how a vulnerable site can be exploited to log in as someone else. Stay tuned! 🕵️♂️
@bryanbrake.bsky.social you may be interested in this starter pack.
@jameskettle.com has put together a great starter pack for bug bounty hunters and InfoSec creators on BlueSky. #infosec #bugbounties #contentcteators
go.bsky.app/GD7hKPX