
Introducing PingOneHound! This OpenGraph extension for BloodHound can help you identify, analyze, execute, and remediate attack paths in PingOne organizations. Read the introductory blog post here: specterops.io/blog/2025/10...

Introducing PingOneHound! This OpenGraph extension for BloodHound can help you identify, analyze, execute, and remediate attack paths in PingOne organizations. Read the introductory blog post here: specterops.io/blog/2025/10...

The AD CS security landscape keeps evolving, and so does our tooling. 🛠️
Valdemar Carøe drops info on Certify 2.0, including a suite of new capabilities and refined usability improvements. ghst.ly/45IrBxI
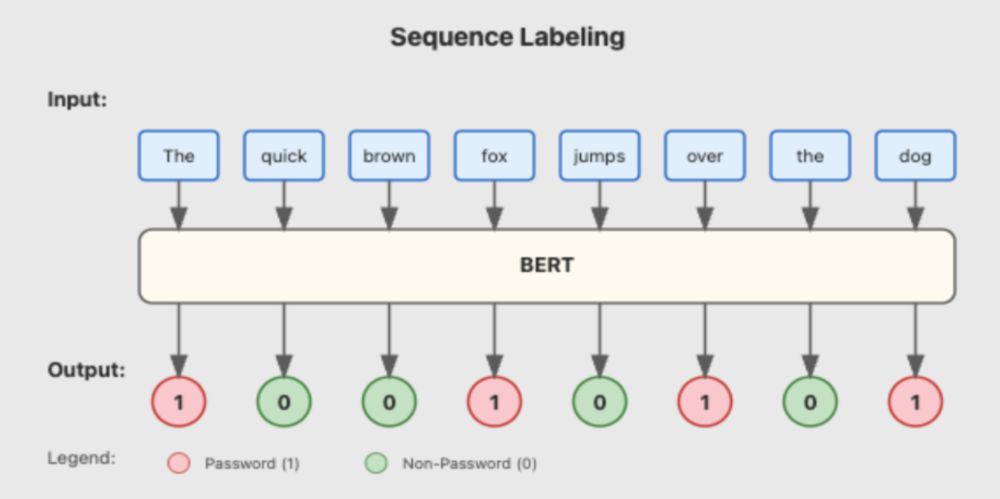
Red teamers know the drill: endless file churning, hunting for passwords & tokens. 🔍
Meet DeepPass2, our new secret scanning tool that goes beyond structured tokens to catch those tricky free-form passwords too. Read Neeraj Gupta's blog post for more. ghst.ly/40HLNNA
The best creds are the ones you simply ask for =)
specterops.io/blog/2025/07...

Finally putting out my research from this spring. "Imitune" coming in soon to support the POC
specterops.io/blog/2025/07...

If you're a #bloodhound user, JD's bloodhound operator is invaluable. Now with opengraph cmdlets!
github.com/SadProcessor...

Looks like the Entra QR code authentication method is going GA 🥳
They've also added some great guidance on suppressing the camera permission prompt for iOS :)
learn.microsoft.com/...
Part 8053 of eleventy billion on our path to killing NTLM: way way way way way better auditing.
support.microsoft.com/en-us/topic/...
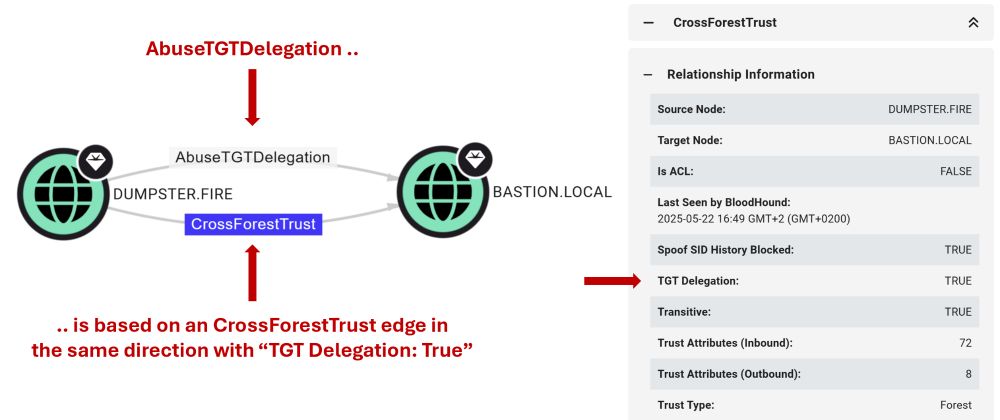
I publish two blog posts today! 📝🐫
First dives into how we're improving the way BloodHound models attack paths through AD trusts: specterops.io/blog/2025/06...
Second covers an attack technique I came across while exploring AD trust abuse: specterops.io/blog/2025/06...
Hope you enjoy the read 🥳
My second post for the month is now live 🎉

A little over a year ago I published research on how you could leverage non-production AWS API endpoints to enumerate permissions without logging to CloudTrail. A year later...I'm still finding them. Red Teamers, these can be super useful and really up your game!
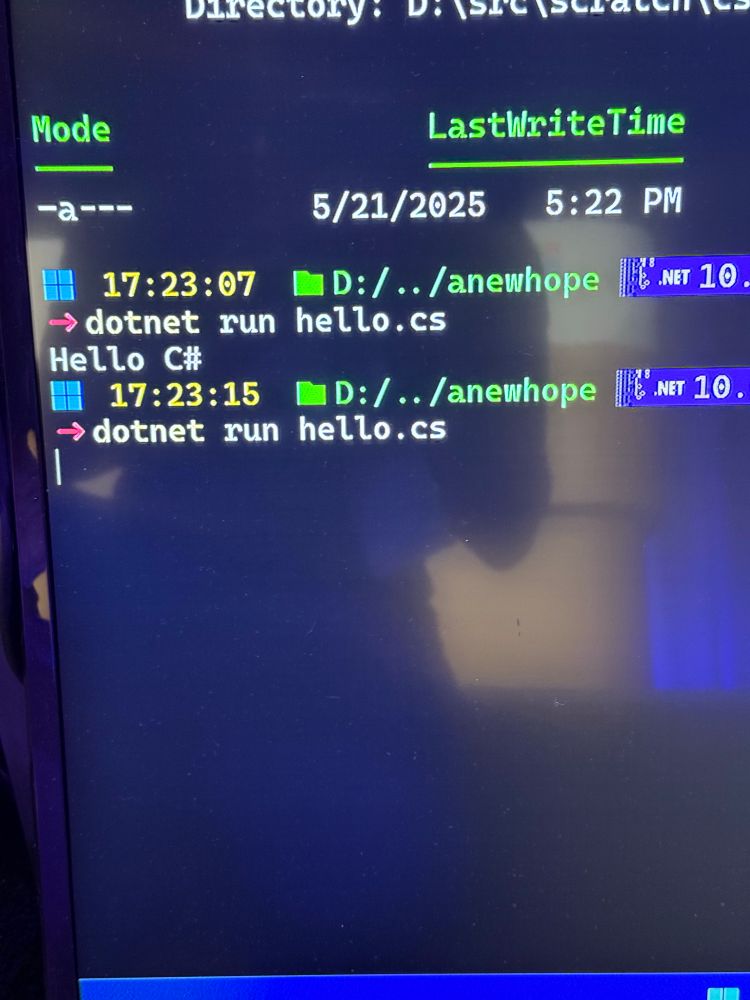
A command line interface
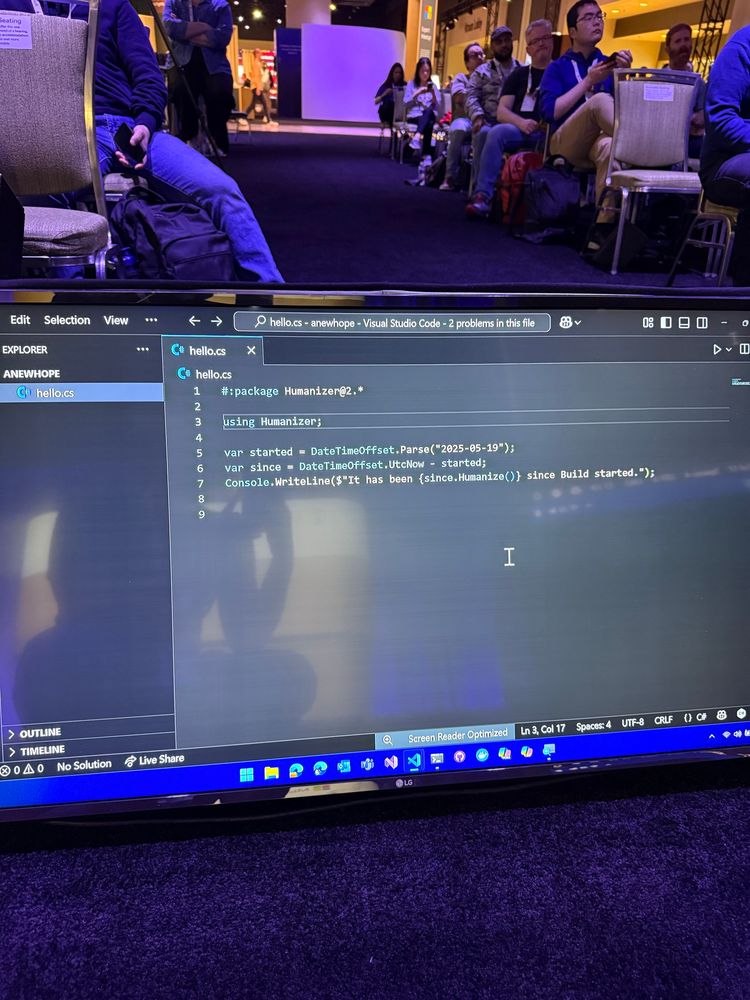
Some c# code
We’re about to take C# to the next level!
#dotnet #csharp
Did you miss #SOCON2025? Did you have a favorite talk you'd like to rewatch?
🎥 All presentations from SO-CON 2025 are now live at ghst.ly/socon25-talks.
💻 Slides for each talk are available at ghst.ly/socon25-slides.

Application Based Authentication on Microsoft Entra Connect Sync is near. With this change you will be able to use a TPM backed certificate in Entra Connect Sync for authentication.
This is a welcome change to prevent the compromise of this high privileged account.
#Entra #Certificate

Did you know you can send LAPS passwords to Entra on Server OS? Neither did @adamgrosstx.bsky.social or I until yesterday! Just need to hybrid join the server(s) and set the GPO to backup to "AAD"! Neat!
Can you use the on-behalf-of flow to bypass conditional access policies? If the middleware app satisfies conditional access, can it exchange an access token to an otherwise blocked backend resource? It turns out... no. No it can't. The CAP will kick in when the middleware app uses the OBO flow.

A new dedicated resource application to enable Active Directory to Microsoft Entra ID sync using Microsoft Entra Connect Sync or Cloud Sync is coming 😱
In the announcement the mentioned reason is "upcoming security hardening"...
6bf85cfa-ac8a-4be5-b5de-425a0d0dc016
#EntraID
🚨 Join the #PeoplesMovement this Saturday #April19 for a National Day of Action!
Yes, people will be in the streets again. Others will be organizing food drives, volunteering at shelters, hosting teach-ins, and more.
Hundreds of events are already listed at www.FiftyFifty.one/events.

Understanding Windows access tokens could be your best defense. At @cackalackycon.bsky.social, @atomicchonk.bsky.social will be peeling back the layers on potato exploits that threat actors use for privilege escalation.
Check out the schedule to learn more ➡️ ghst.ly/4jzjlnI
Had some fun with PDQ deploy/inventory credential decryption and wrote about it here: unsigned-sh0rt.net/posts/pdq_cr... thanks to
@dru1d.bsky.social for writing a BOF out of the POC
tl;dr get admin on PDQ box, decrypt privileged creds

Everybody’s using AI assistants and tools these days, but do most of us understand how our text-based input is being interpreted and processed? Check out my latest blog post for a basic intro to text interpretation by AI assistants. www.corgi-Corp.com/post/tokeniz...
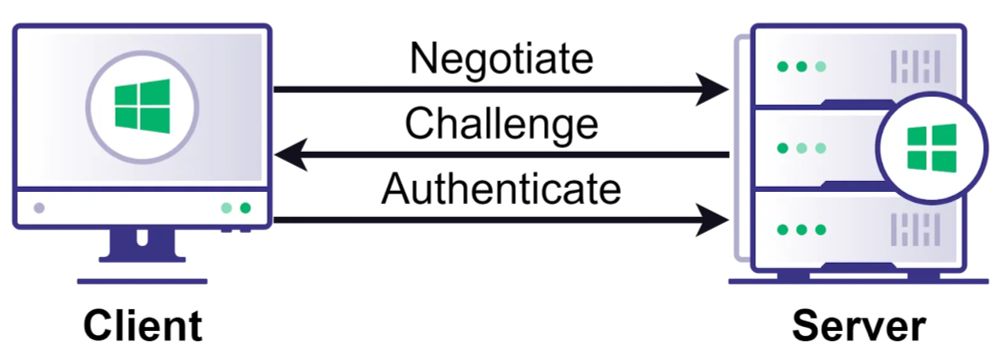
Think NTLM relay is a solved problem? Think again.
Relay attacks are more complicated than many people realize. Check out this deep dive from Elad Shamir on NTLM relay attacks & the new edges we recently added to BloodHound. ghst.ly/4lv3E31

Nothing new, but formalized some operator notes on Entra ID/Azure tradecraft I've found to be exceptionally useful on ops. Overlooked this myself for quite some time and thought others in the same boat might find it worth a read! 📖
medium.com/specter-ops-...

1 year anniversary at SpecterOps, so many personal and professional achievements in a short space of time. My advice for anyone getting into this field, try and make sure that you work companies and colleagues that push you beyond your comfort level. \o/

We are excited to see everyone at #SOCON2025 tomorrow! 🙌
Get the details on everything you need to know before arriving at the conference: specterops.io/so-con

Spent the evening deep diving into MCPs and started a new project: roadrecon_mcp_server! This #MCP takes the web GUI output from the awesome ROADtools by @dirkjanm.io and offers tools to Claude (or your #AI agent of choice) to interact with the data:
github.com/atomicchonk/...
What's the purpose of the x-ms-DeviceCredential header if the device id claim is already included in the user access token? It seems redundant
🎙️ BIG NEWS: I'm launching Entra.Chat - the podcast identity pros have been waiting for!
After years in the identity trenches, I've seen a lot - the midnight calls, the authentication puzzles, and those "how is this even possible?" moments.
Has anyone heard of anyone actually setting up WHFB certificate trust? it's gotta be a MS troll