Using Github mirror instead of docker.io:
FROM mirror.gcr.io/{image_name}
#dockeroutage
Using Github mirror instead of docker.io:
FROM mirror.gcr.io/{image_name}
#dockeroutage

Phishing E-Mail using Github issue notification through mention redirecting
2FA reset phishing seems to be quite a thing right now
I’ve been diving deeper into the WebAssembly Component Model lately, and I finally sat down to write up a hands-on example in Rust.
It’s a small example, but for me it really clarified how the component model makes composition and reuse feel natural.
👉 m99.io/articles/cre...
#wasm #rust
I didn't have brew cleanup on the radar yet. It freed almost 80 GB of unused packages
Redmine is so much more practical than Jira. Especially for issue tracking and it even allows cascading subtasks. The only major downside I see is the Wiki because editing is not in-place. Also post-configuring the Postgres tables was needed for me (utf8mb4) to allow Emojis in issue texts
Now that Let's Encrypt stopped their notification mails I just swapped nginx for Caddy which automagically handles certificates
IMHO the best tool to organize source installations on Linux: GNU Stow (unless using an immutable distribution like NixOS...)
Running nginx with HTTP/3 is quite adventurous. I appreciate though that (the required) compiling from source allows me to use LibreSSL
I always create a function Main() (err error) that I call from main. Mostly out of convenience though to be able to just write "return" for error checking
Vulnerability websites with logos seem to have fully superseded CVE numbers by now
I don't like the clunkiness of Dependency Injection but every time I'm surprised how test coverage increases almost by itself
Underrated file system protocol: WebDAV
Self-hosting E-Mail has come a long way. That's my second attempt now, this time with Mox. A few months aren't really enough data points but at this point it's already more reliable than Protonmail
To create a systemd user service:
• service definition in /home/username/.config/systemd/user/
• using target default (multi-user won't work on boot)
• loginctl enable-linger username
• systemctl --user enable my.service
(Optionally systemctl --user daemon-reload with XDG_RUNTIME_DIR set)
I tried the Vault Secrets Operator recently and once the setup is done, it's really practical. Also automated secret rotation is quite something. #kubernetes #vault
Current versions of WebPageTest are quite practical. Apart from the usual performance insights it also has now carbon control and an accessibility check.
Google enforcing JS enabled browsers reminds me of a discussion I had 11 years ago on the PhantomJS mailing list asking whether it adheres to robots.txt.
The answer was no, also with the argument that it's not a bot and scriptable like a Browser.
I still find it quite an interesting perspective.
I'd also add regularly cleaning the nozzle (watch out, it's hot) before problems occur, just with Isopropyl alcohol and a paper towel. There are plenty of guides how to do this though.
I see, that's not ideal. (I somewhat liked the standardization effort of the Filesystem hierarchy though while it was current but I guess that's only a small bit of it.)
I cannot believe the Linux Standard Base has been abandoned. (Paradoxically Linux on the Desktop is as popular as never before.) #linux
Using runtime.LockOSThread() is a nice trick to prevent unpredictable results when using #cgo or doing syscalls in #golang
How important is Rowhammer in the real world? Seems it'll be a bit more certain next year #38c3 flippyr.am
Happy holidays!
![Go example that imports a library with a vulnerable accept header parser function from 2020. It uses the reflect package to call it. Running govulncheck in binary mode results in finding 2 vulnerabilities.
Source code:
```
$ cat main.go
package main
import (
"golang.org/x/text/language" // v0.3.4 (2020)
"reflect"
)
func Main() {
language.ParseAcceptLanguage("00-t-0o")
}
func main() {
reflect.ValueOf(Main).Call([]reflect.Value{})
}
```](https://cdn.bsky.app/img/feed_thumbnail/plain/did:plc:qazna4xgil7x3nedsqrjd7b7/bafkreich5bzlowxndlqbtebn5bl6riidon726usef4sjg7ykzgo7ddks2e@jpeg)
Go example that imports a library with a vulnerable accept header parser function from 2020. It uses the reflect package to call it. Running govulncheck in binary mode results in finding 2 vulnerabilities. Source code: ``` $ cat main.go package main import ( "golang.org/x/text/language" // v0.3.4 (2020) "reflect" ) func Main() { language.ParseAcceptLanguage("00-t-0o") } func main() { reflect.ValueOf(Main).Call([]reflect.Value{}) } ```
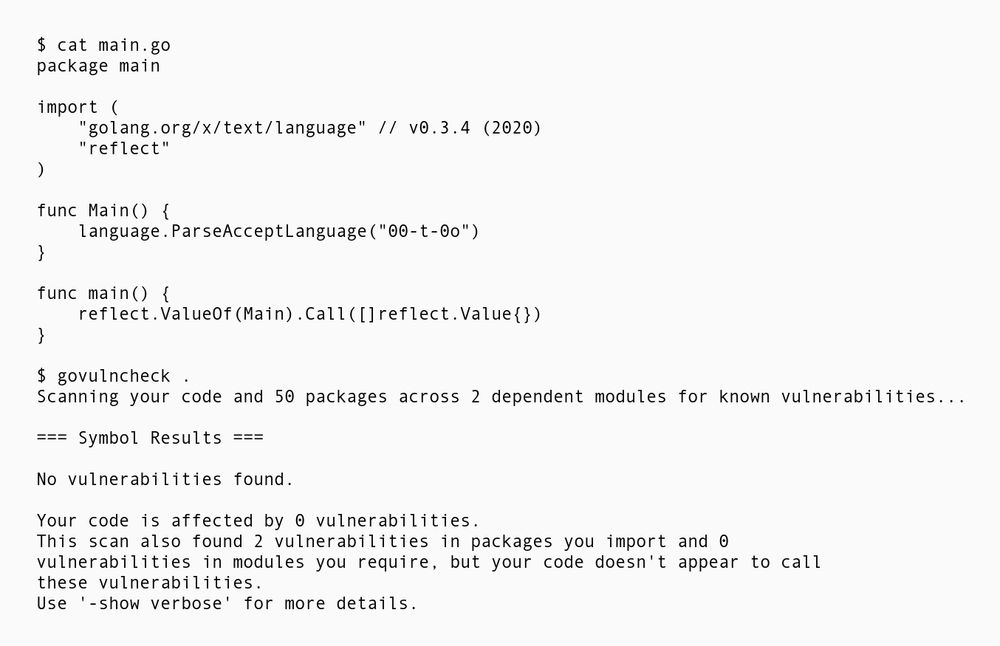
Again the same Go example calling a vulnerable function using reflect. This time govulncheck is called in source mode though, reporting: No vulnerabilities found. Your code is affected by 0 vulnerabilities. This scan also found 2 vulnerabilities in packages you import and 0 vulnerabilities in modules you require, but your code doesn't appear to call these vulnerabilities.
govulncheck also has a binary mode to increase coverage for reflect based call chains #devsecops #golang
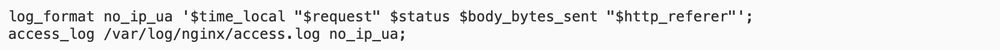
log_format no_ip_ua '$time_local "$request" $status $body_bytes_sent "$http_referer"'; access_log /var/log/nginx/access.log no_ip_ua;
Logging in nginx without IP and User-Agent when feasible
Keeping dependency count low and sticking to high quality dependencies at the beginning of a project has multiplier effects. Upgrading to recent versions is feasible when done consistently. Thus keeping security in check and preventing package archeology during migrations #devsecops #shiftleft
Microservices all the way 😀 I'm playing around with Next at the moment but I cannot decide yet. If anything more complex is needed Backend-wise, I rather put that into a separate service though
My favorite hosters are actually Hetzner and Scaleway. For instance Scaleway feels very round and I'm impressed that they use resource efficient adiabatic cooling in PAR2 which reduces water usage
Something random like UUID is definitely an advantage security-wise, e.g. to prevent enumeration attacks (definitely need to look into ULID, first time I hear about them)