Oh I nearly forgot about this platform
29.01.2026 20:22
👍 4
🔁 0
💬 0
📌 0

Sign in as anyone: Bypassing SAML SSO authentication with parser differentials
Critical authentication bypass vulnerabilities were discovered in ruby-saml up to version 1.17.0. See how they were uncovered.
If you're using ruby-saml or omniauth-saml for SAML authentication make sure to update these libraries as fast as possible! Fixes for two critical authentication bypass vulnerabilities were published today (CVE-2025-25291 + CVE-2025-25292).
github.blog/security/sig...
12.03.2025 21:50
👍 11
🔁 10
💬 1
📌 0
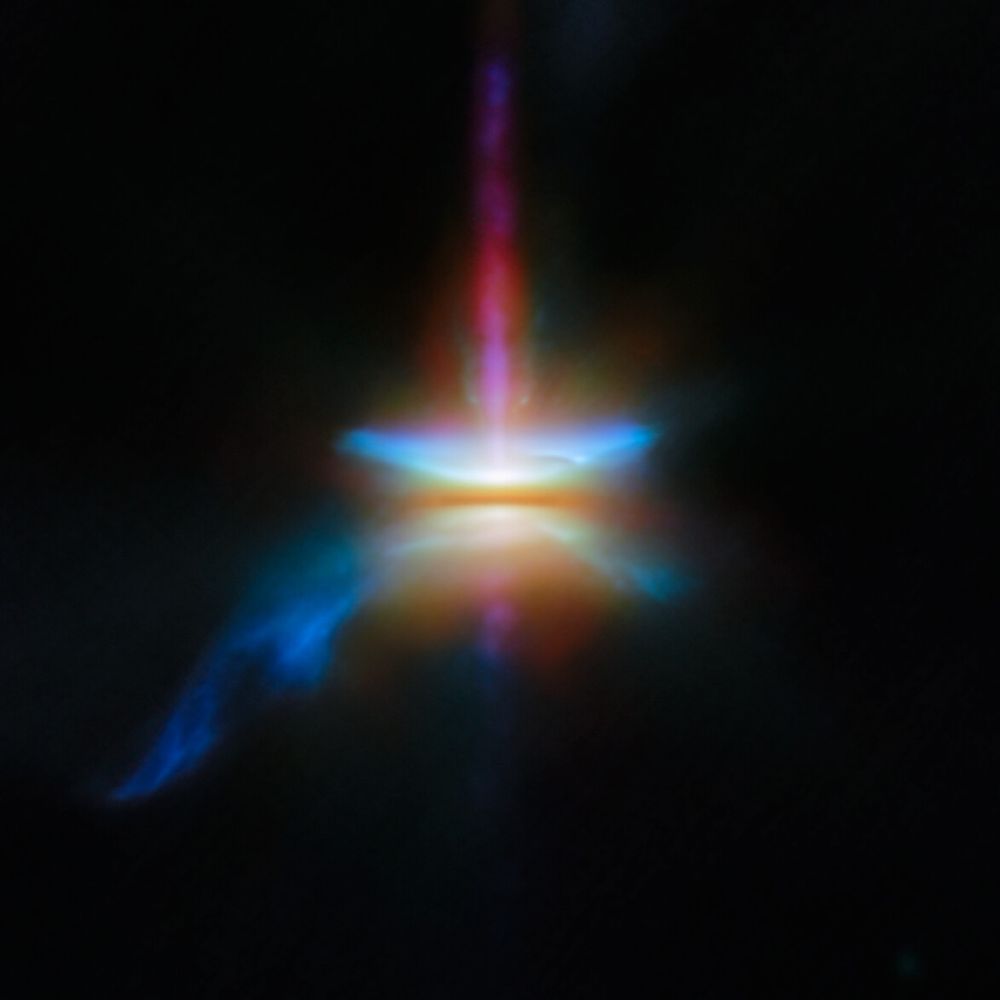
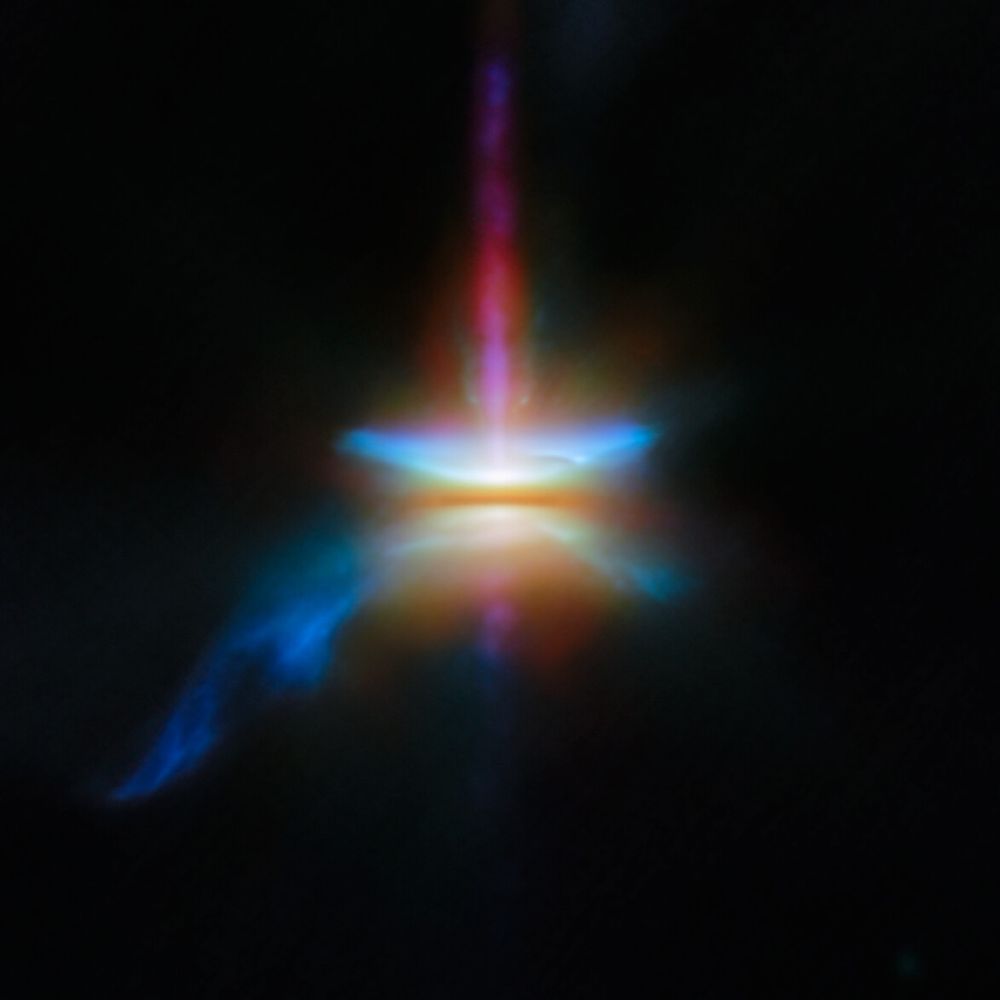
A close-in image of a protoplanetary disc around a newly formed star. Many different wavelengths of light are combined and represented by separate and various colors. A dark line across the center is the disc, made of opaque dust: the star is hidden in here and creates a strong glow in the center. A band going straight up is a jet, while other outflows form flares above and below the disc, and a tail coming off to one side.
NEW JWST IMAGE SHOWING A PROTOPLANETARY DISK AROUND A NEWLY FORMED STAR!!! 🤩
05.02.2025 00:00
👍 1017
🔁 210
💬 30
📌 12

Last year, I committed to uncovering critical vulnerabilities in Maven repositories. Now it’s time to share the findings: RCE in Sonatype Nexus, Cache Poisoning in JFrog Artifactory, and more! github.blog/security/vul...
22.01.2025 18:16
👍 28
🔁 16
💬 1
📌 0
Abstaining From Pwn2own – muffSec
This is what I love about Chris, authenticity: muffsec.com/blog/abstain.... Btw I couldn’t agree more with his conclusion about the event.
22.01.2025 09:37
👍 3
🔁 0
💬 0
📌 0
Bitcoin is enemy of culture because it introduces monetary incentive where only prestige belongs.
17.01.2025 18:13
👍 175
🔁 16
💬 2
📌 1
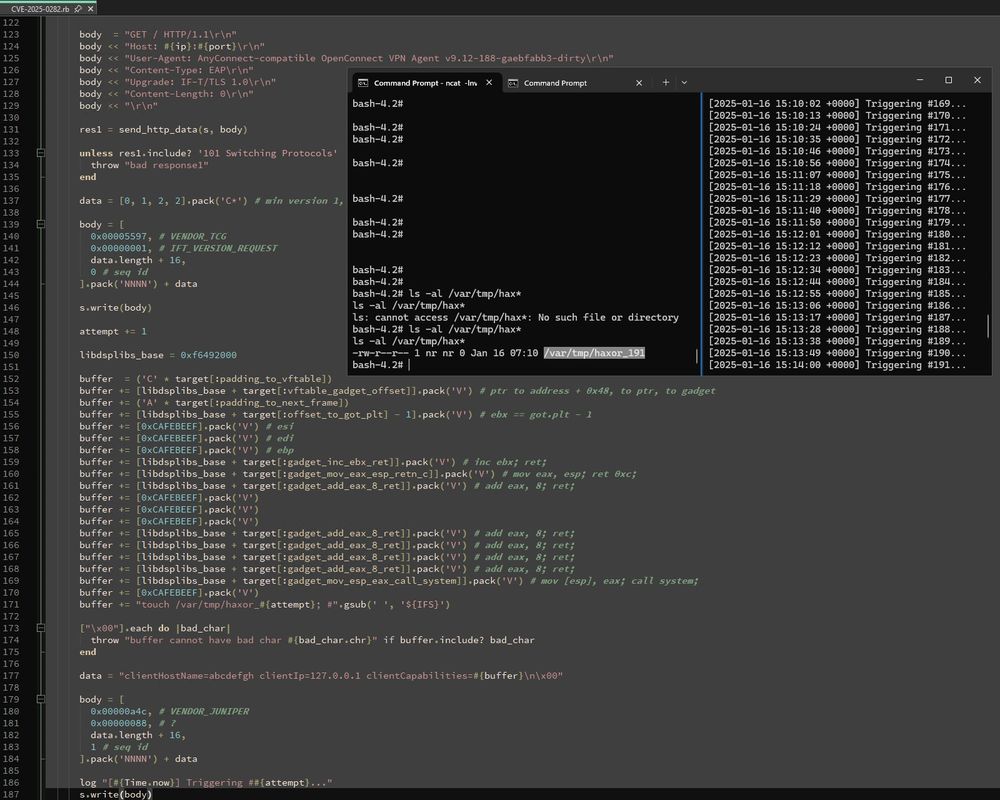
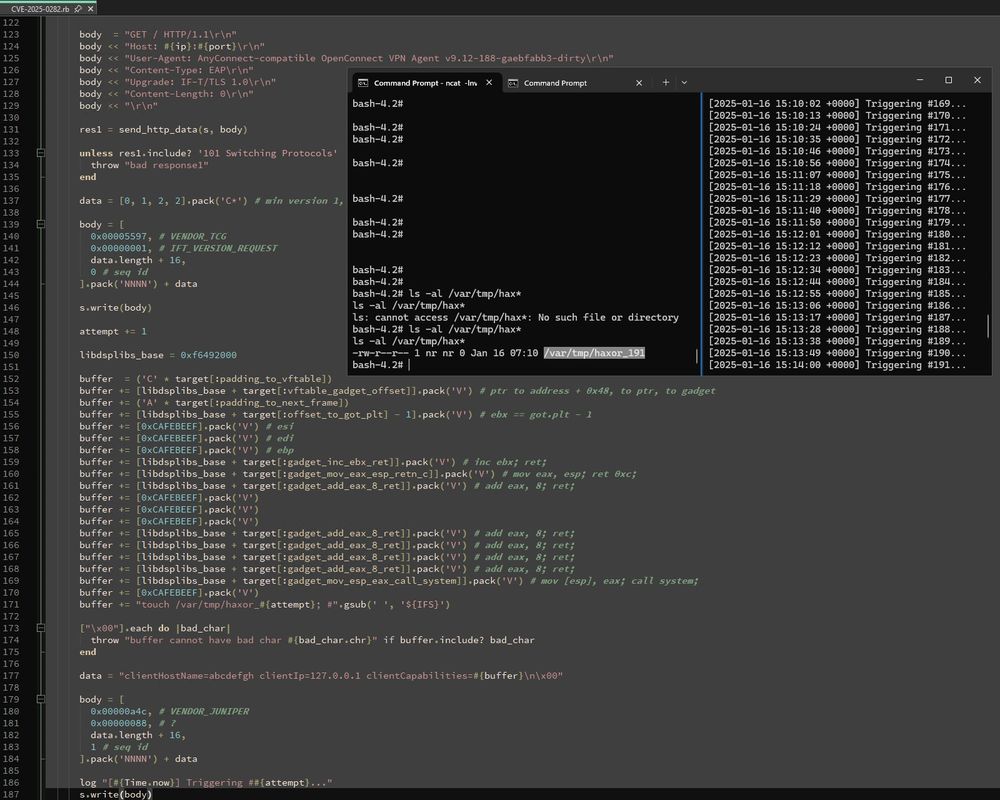
I wrote a PoC for the recent Ivanti Connect Secure stack buffer overflow, CVE-2025-0282, based on the exploitation strategy watchTowr published, along with an assessment of exploitability given the lack of a suitable info leak to break ASLR: attackerkb.com/assessments/...
16.01.2025 15:52
👍 11
🔁 8
💬 1
📌 0
What's the point of being rich if you can't afford to do the right thing.
13.01.2025 16:29
👍 27439
🔁 4139
💬 734
📌 239
Project Zero
Just unrestricted an issue that shows a fun new attack surface. Android RCS locally transcribes incoming media, making vulnerabilities audio codecs now fully-remote. This bug in an obscure Samsung S24 codec is 0-click
project-zero.issues.chromium.org/issues/36869...
10.01.2025 00:08
👍 38
🔁 16
💬 1
📌 2
Aleph Bass — an aleph bet song by Darshan :: אלף בית – דרשן
YouTube video by Darshan Project
youtu.be/a6EnyQ0Dy50?...
03.01.2025 21:14
👍 1
🔁 0
💬 0
📌 0
Positive Technologies published two scenarios they encountered during pentests, where they pivot to the internal network thanks to an Internet-facing Exchange server and its numerous SSRF vectors 💎
27.12.2024 13:39
👍 6
🔁 3
💬 1
📌 0
Nice fail troll
27.12.2024 04:15
👍 0
🔁 0
💬 0
📌 0
TIL how easy it is to ask curl to dump TLS session keys to disk 🛠️
Simply set the environment variable `SSLKEYLOGFILE=/path/to/file` 😅 Note: it also works for Firefox and Chrome
Extremely useful when combined with Wireshark 👍
20.12.2024 11:35
👍 134
🔁 36
💬 6
📌 0
CVE-2024-12727 Sophos coming in with an unauthenticated SQLi in their firewall appliance 👏
22.12.2024 08:43
👍 93
🔁 26
💬 2
📌 5

Life doesn’t need to be complicated
22.12.2024 04:56
👍 2
🔁 0
💬 0
📌 0
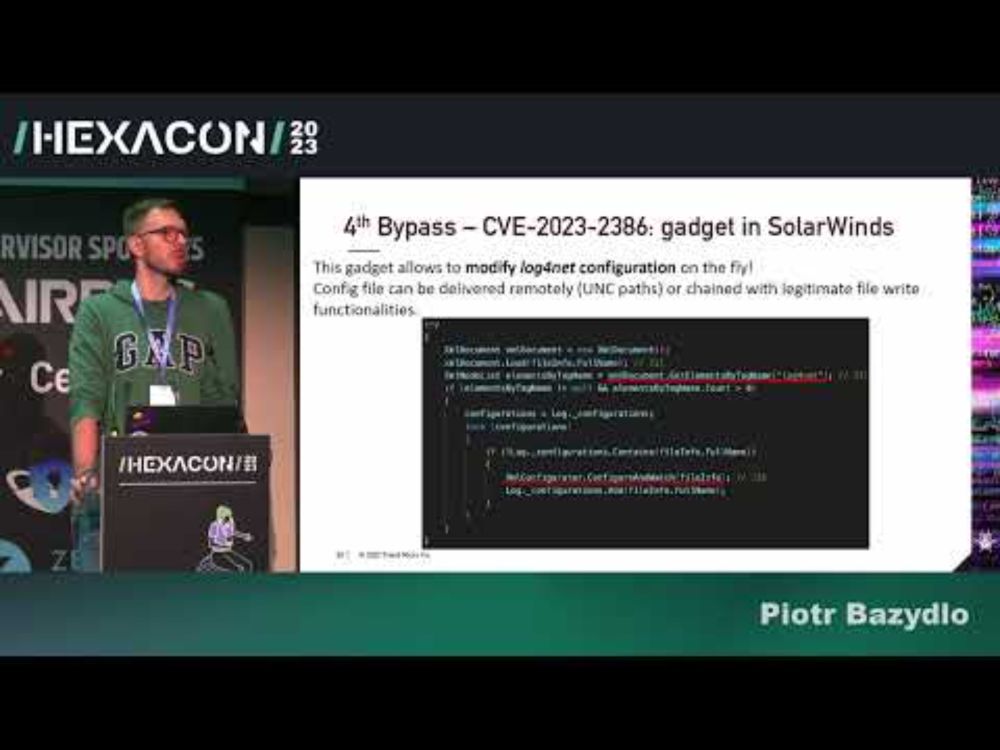
HEXACON2023 - Exploiting Hardened .NET Deserialization by Piotr Bazydło
YouTube video by Hexacon
[4/n] My Hexacon 2023 talk about .NET Deserialization. New gadgets, insecure serialization (RCE through serialization) and custom gadgets found in the products codebase.
Talk: www.youtube.com/watch?v=_CJm...
White paper: github.com/thezdi/prese...
19.12.2024 11:39
👍 5
🔁 2
💬 0
📌 0
I put together a VERY limited (for now) list of web hackers in a Starter pack:
go.bsky.app/9uay4Ad
A lot of people are missing (I will try to add more as I find them) but make sure you follow people already in the list!
18.12.2024 00:54
👍 30
🔁 13
💬 3
📌 0
It’s a different poc per app that’s vulnerable. Most struts apps that use a vuln framework are probably not vuln because they still need to implement an upload feature in a specific way. TL;DR don’t lose sleep over it.
18.12.2024 19:40
👍 3
🔁 1
💬 1
📌 0
S2-067 is a fantastic bypass of the patch for S2-066. It uses ONGL to re-write the upload filename property in order to bypass the filename path traversal checks.
PoC: if the target bean is called "UploadFile" the your target parameter is "top.UploadFileFileName". 🤯
17.12.2024 20:29
👍 6
🔁 2
💬 0
📌 0
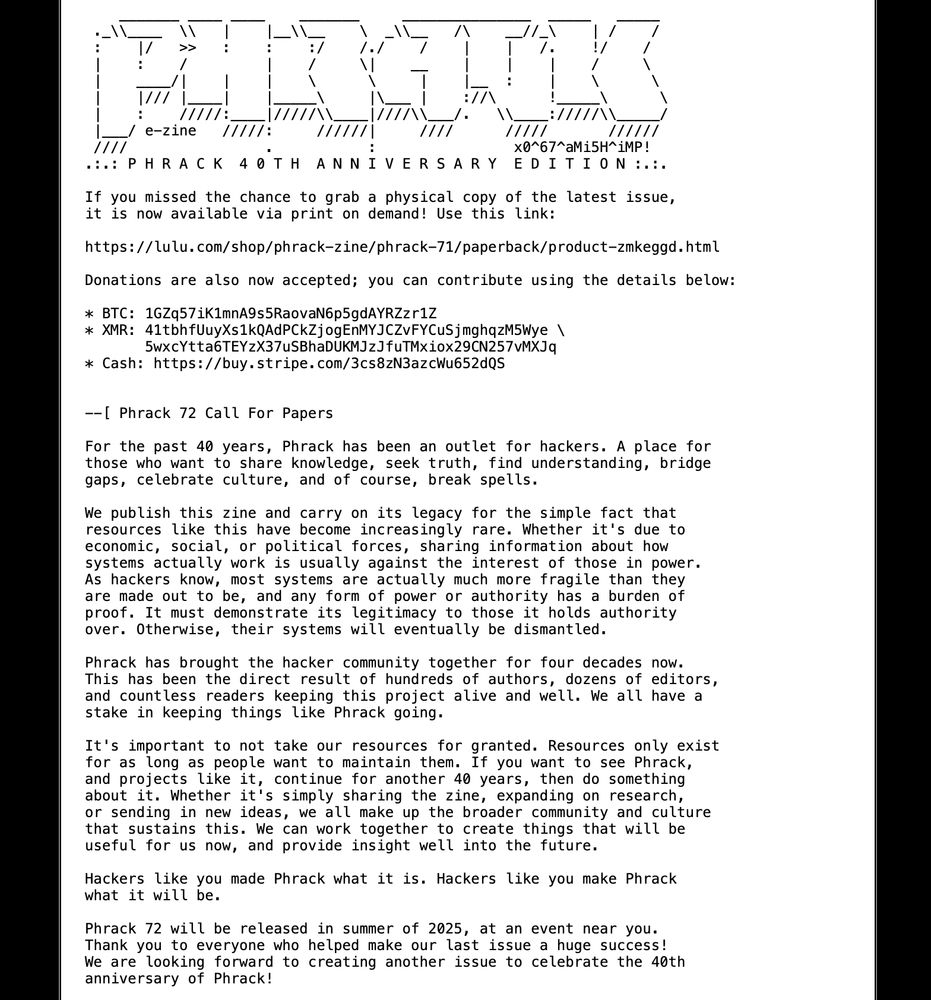
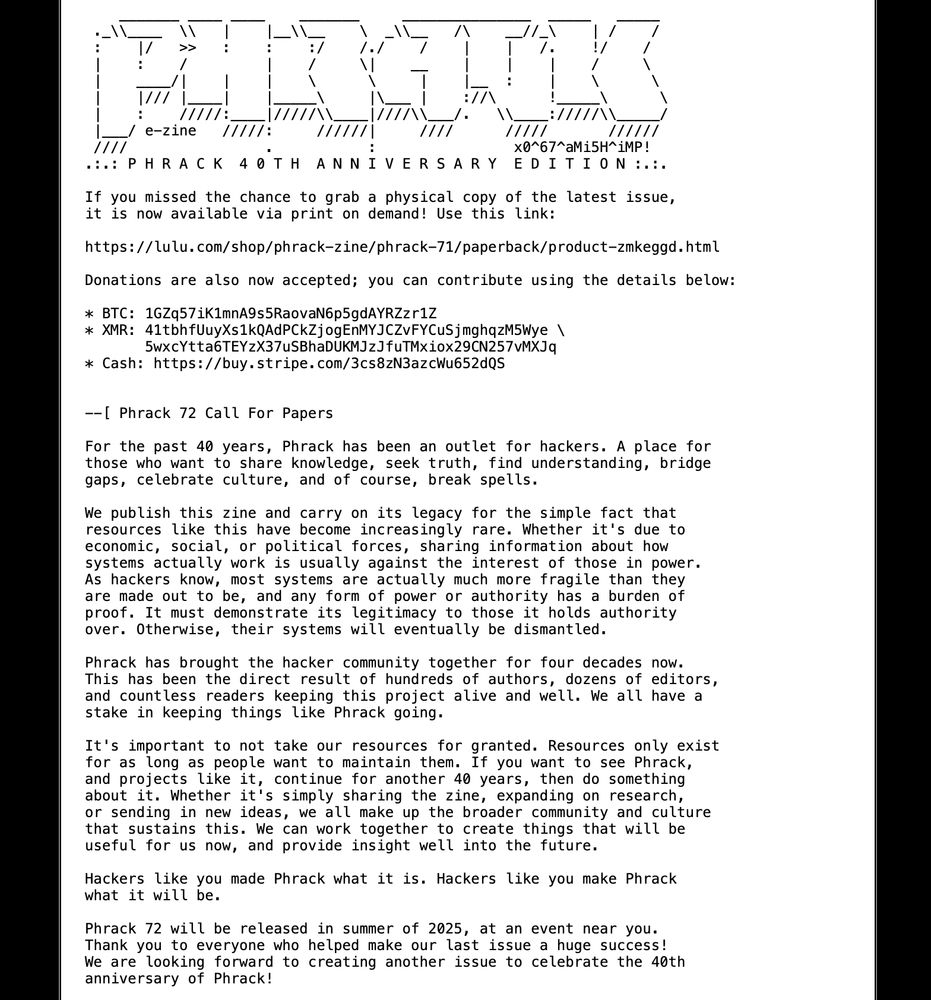
screenshot of the CFP on phrack.org
We updated our CFP for Phrack 72! The deadline is now April 1st 2025. Check the site for specifics on how to contribute, as well as some inspiration! We also posted a link to purchase physical copies of Phrack 71, and a donation link too. Enjoy!
phrack.org
16.12.2024 22:56
👍 114
🔁 58
💬 4
📌 4

wokism is out of control
17.12.2024 05:21
👍 6946
🔁 373
💬 102
📌 13
…and what is your office? My office is that which is in the higher aspirant of the soul - Ma’at
16.12.2024 23:05
👍 0
🔁 0
💬 0
📌 0
Mexico is always a good idea, though I maybe biased :D
16.12.2024 02:13
👍 3
🔁 0
💬 0
📌 0
A companion blog to my Bluehat 2024 presentation on OleView.NET is up now. googleprojectzero.blogspot.com/2024/12/wind...
12.12.2024 23:32
👍 20
🔁 12
💬 0
📌 1